Enterprise Security Operations
Comprehensive security infrastructure and SOC services designed to protect your organization from evolving cyber threats through defense-in-depth strategies
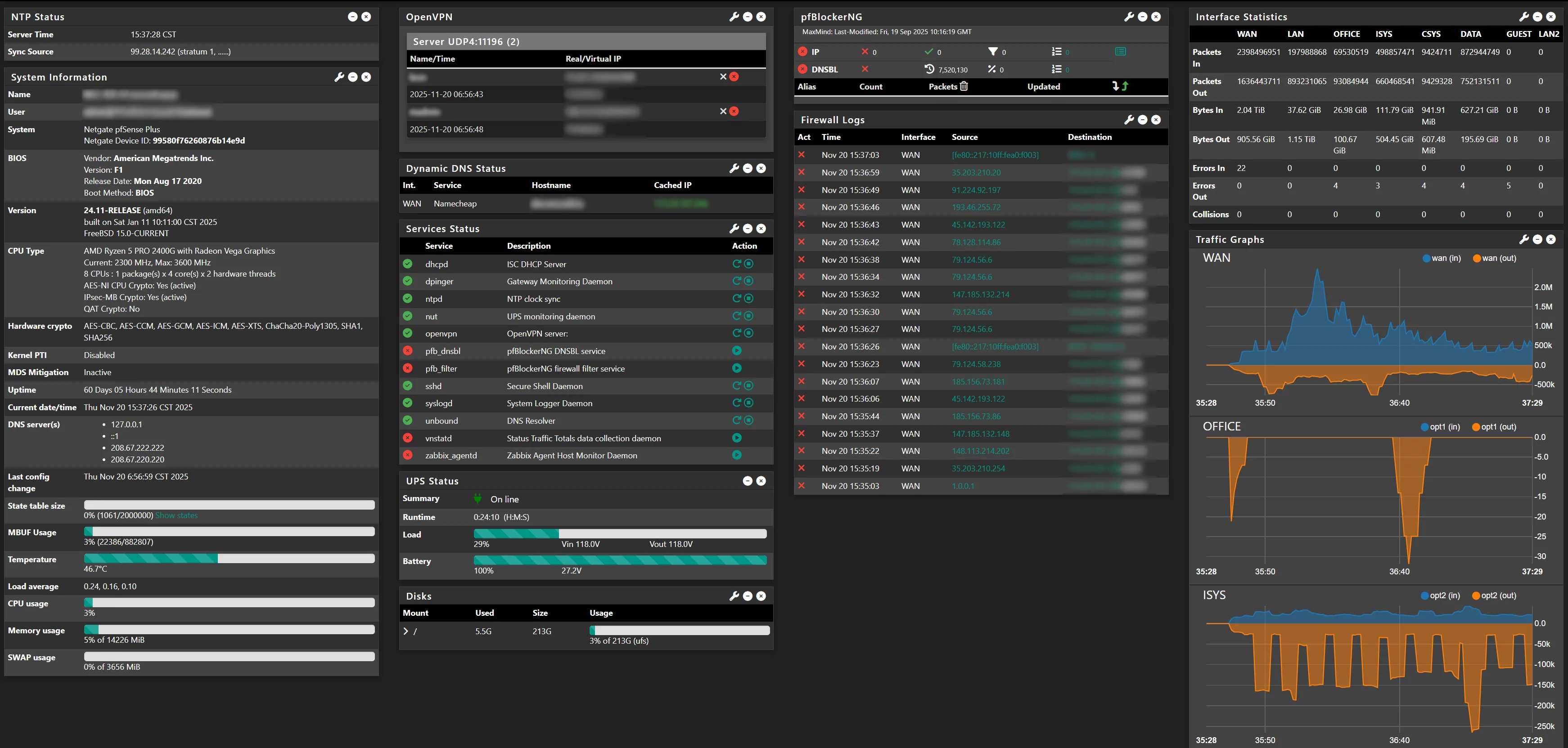
Advanced Firewall Management
Enterprise-grade network security utilizing pfSense for comprehensive perimeter defense and traffic management
Our firewall solutions provide robust network security through sophisticated rule sets, traffic shaping, and multi-layered defense strategies. We deploy and manage pfSense firewalls configured for high-availability, ensuring your network remains secure while maintaining optimal performance.
Firewall Capabilities
- pfSense deployment and configuration
- Stateful packet inspection and filtering
- High-availability (HA) firewall clustering
- VPN concentrator (IPsec, OpenVPN, WireGuard)
- Traffic shaping and QoS implementation
- NAT, port forwarding, and routing optimization
- Real-time firewall log analysis and alerting
Security Features
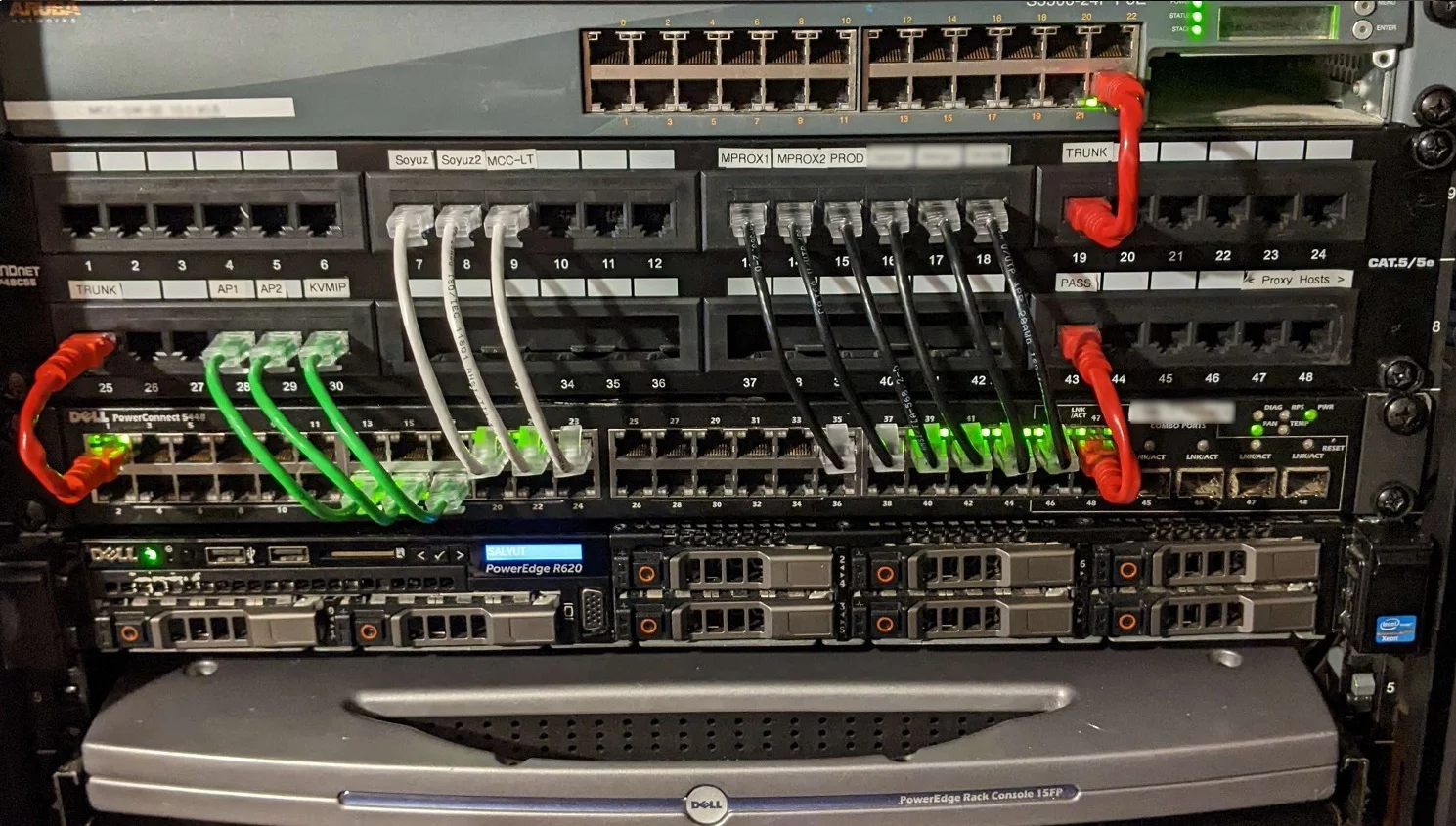
VLAN Architecture & Segmentation
Strategic network segmentation isolating critical systems and reducing lateral movement risk
Proper network segmentation is fundamental to defense-in-depth security. We design and implement sophisticated VLAN architectures that isolate critical systems, segment user populations, and control inter-VLAN traffic through carefully crafted access control lists and routing policies.
Segmentation Strategy
- Zero-trust network architecture design
- VLAN segmentation and isolation planning
- Inter-VLAN routing and ACL implementation
- Guest network isolation with captive portals
- VLAN tagging and trunk configuration
- Private VLAN (PVLAN) implementation
- Micro-segmentation for critical assets
Network Zones
Corporate VLAN
Internal user workstations
Server VLAN
Production infrastructure
Database VLAN
Sensitive data stores
Vendor VLAN
Third-party access
Management VLAN
Infrastructure admin access
Guest Networks
Isolated visitor access
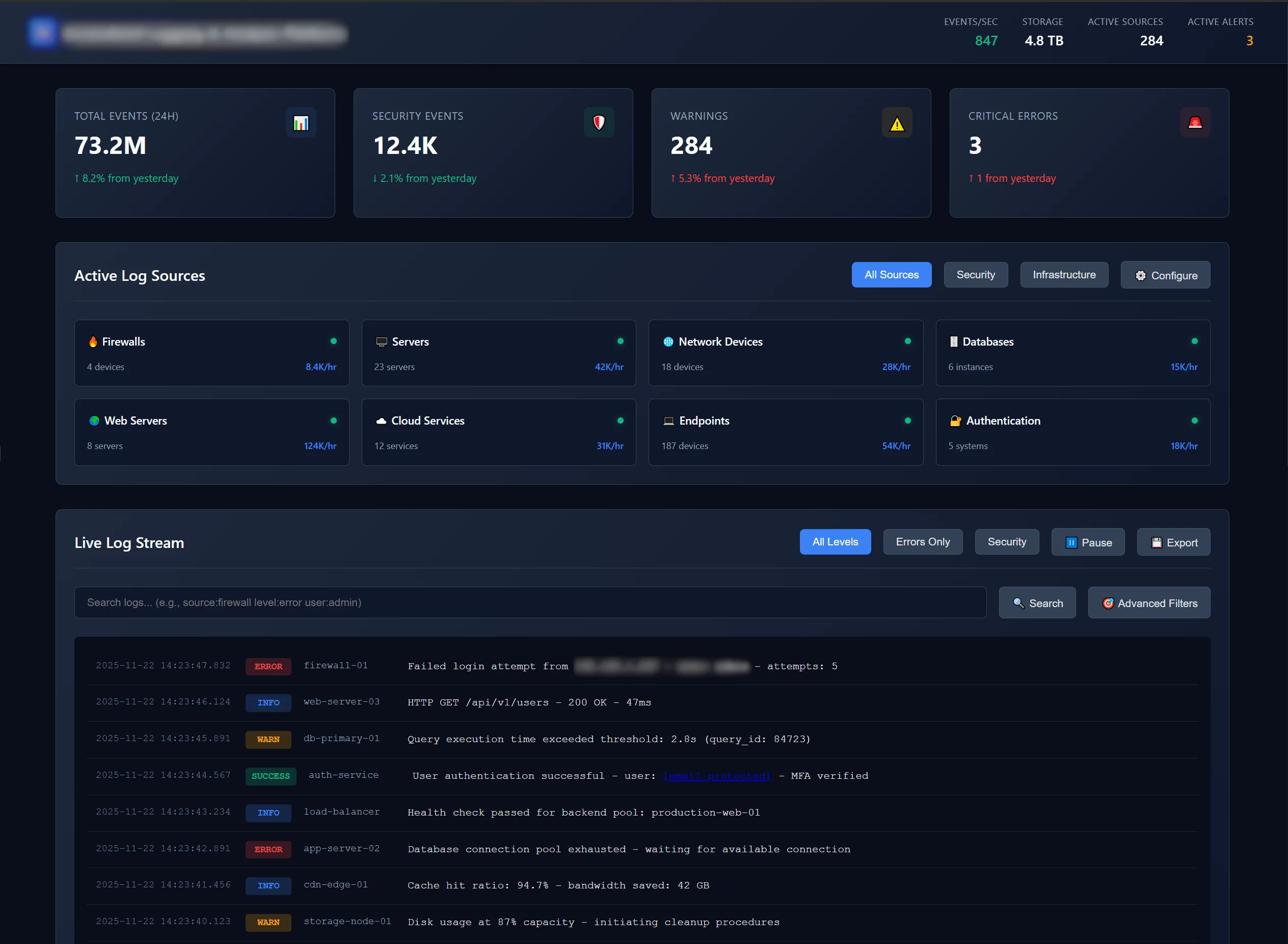
Centralized Logging & Analysis
Comprehensive log collection, retention, and analysis supporting security investigations and compliance
Effective security monitoring requires comprehensive logging from all critical systems. We implement centralized log management solutions that collect, parse, and analyze logs from firewalls, servers, applications, and security tools. Long-term log retention supports both security investigations and regulatory compliance requirements.
Logging Infrastructure
- Centralized syslog collection and aggregation
- Log parsing and normalization
- Long-term log retention and archival
- Real-time log analysis and correlation
- Custom dashboards and visualizations
- Automated alerting on security events
- Compliance reporting (PCI DSS, HIPAA, SOC 2)
- Forensic search and investigation tools
Log Sources
Secure Your Enterprise Infrastructure
Protect your organization with comprehensive security operations backed by industry-leading tools and expertise. Our SOC team is ready to defend your infrastructure 24/7/365.
Request Security Assessment